Two-step verification in Plone 4 using login codes sent by SMS.
Project description
Two-step verification for Plone 4 with use login codes sent by SMS. This app allows users to enable the two-step verification for their Plone accounts. A mobile phone capable to receive SMS messages is obviously required. Usage of two-step verification is optonal, unless site admins have forced it (configurable in app control panel). Admins can white-list the IPs, for which the two-step verification would be skipped.
Prerequiresites
Mobile phone which is able to receive SMS messages.
Plone 4 (tested with Plone >= 4.3.1)
Limitations
Note, that two-step verification works only for Plone users and does not work for Zope users (those added with “./bin/instance” adduser command).
Usage
Case 1: Enabling the two-step verification
Pre-conditions: User is not logged into the Plone site, does not yet have two-step verification enabled and has a mobile phone.
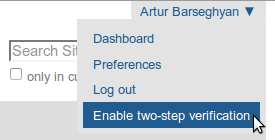
From any page follow the “Enable two-step verification” link in the menu (next to “Log out”).
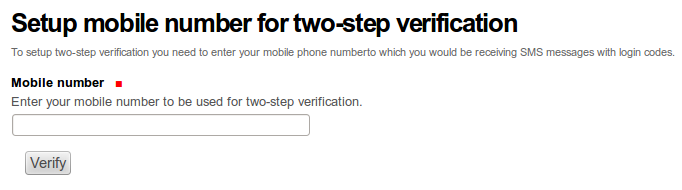
If you haven’t yet filled in your mobile phone number, you will be requested to do so. You will receive immeditely a SMS with confirmation code in.
When you’re done, you get to a page on which you will be requested to enter the code received by SMS.
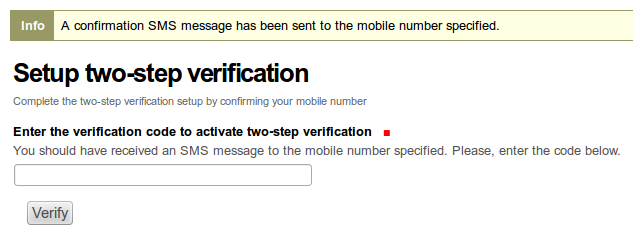
Enter the secret code shown in the “Enter the verification code to activate two-step verification” field for confirmation and press the “Verify” button.
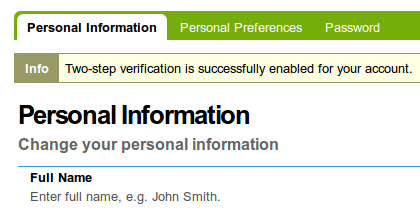
Upon successful confirmation (you should see a message stating that) the two-step verification is enabled for your account.
Case 2: Two-step verification
Pre-conditions: User is not logged in and has enabled the two-step verification.
When you log into the Plone site (just using username and password), you would see an extra screen on which you are asked to provide the login code, sent to your by SMS.
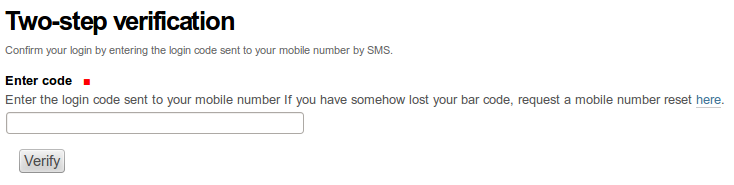
You should then check your phone for the new SMS message and type in the token shown into the “Enter code” field.
If token is valid, you would be logged in.
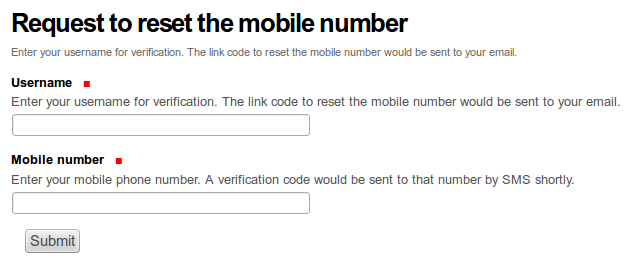
Case 3: Lost mobile phone or phone number
Pre-conditions: User is not logged in, has enabled the two-step verification.
There might be cases when you have lost your mobile phone (either really lost it or broken accident or somehow lost ownership of your former mobile number). For such cases, you can reset the phone number.
Log into the Plone site (just using username and password), for to see the extra screen on which you are asked to provide the login code, sent to your by SMS and follow the link (help text of the “Enter code” field). You would then land on the page where from you can request the mobile number reset.
Enter your username and mobile number in the “Username” and “Mobile number” fields respectively, press the “Submit” button. Link for resetting your mobile number will appear in your mailbox shortly. Having clicked on the link to reset the mobile number, would bring your to a page where you can enter the verification code.
You will receive an SMS with verification code shortly. Enter the code in the “Enter the verification code to activate the two-step verification” field.
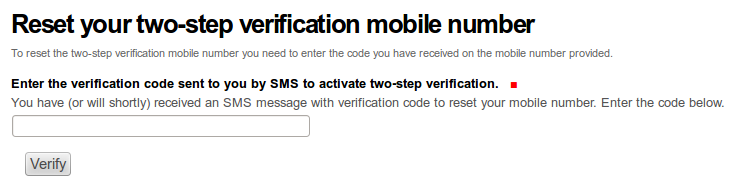
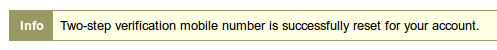
Upon successful confirmation (you should see a message stating that) your mobile number is reset.
Case 4: Disabling the two-step verification
Pre-conditions: User is logged in and has enabled the two-step verification.
From any page follow the “Disable two-step verification” link in the menu (next to “Log out”).
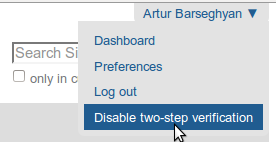
After which you would get a message.
Installation
Buildout
>>> [instance] >>> eggs += >>> collective.smsauthenticator
>>> zcml += >>> collective.smsauthenticator
ZMI
ZMI -> portal_quickinstaller
Choose “SMS Authenticator Plone” and install it.
ZMI -> acl_users
Choose “sms_auth (SMS Authenticator plugin (collective.smsauthenticator))”.
Make sure the “Active plugins” section of “Authentication” has the following plugins in the given order (“sms_auth” should come as first - critical!):
sms_auth
session
source_users
Configuration options
App control panel can be accessed at http://your-plone-site.com/@@sms-authenticator-settings
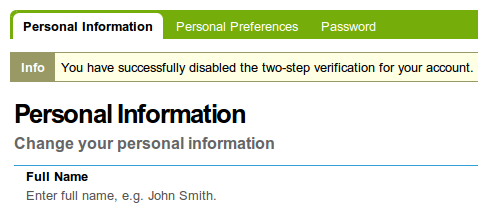
Main
Globally enabled
If checked, two-step verification is globally force-enabled for all site users and they no longer have an option to disable it; this applies to all new users (just registered accounts) as well.
White-listed IP addresses
List of white-listed IP addresses - one at a line. If user comes from one of those, the two-step verification is skipped even if user has enabled it or two-step verification is globally enabled.
Extra
Additionals options of the control panel are:
Enable two-step verification for all users.
Disable two-step verification for all users.
Twilio

Twilio number
Your Twilio AccountSID and AuthToken. Visit your Twilio Account Phone Number page and check the Manage Numbers section.
Twilio AccountSID and Twilio AuthToken
Your Twilio AccountSID and AuthToken. Visit your Twilio Account Settings page and check the API Credentials section.
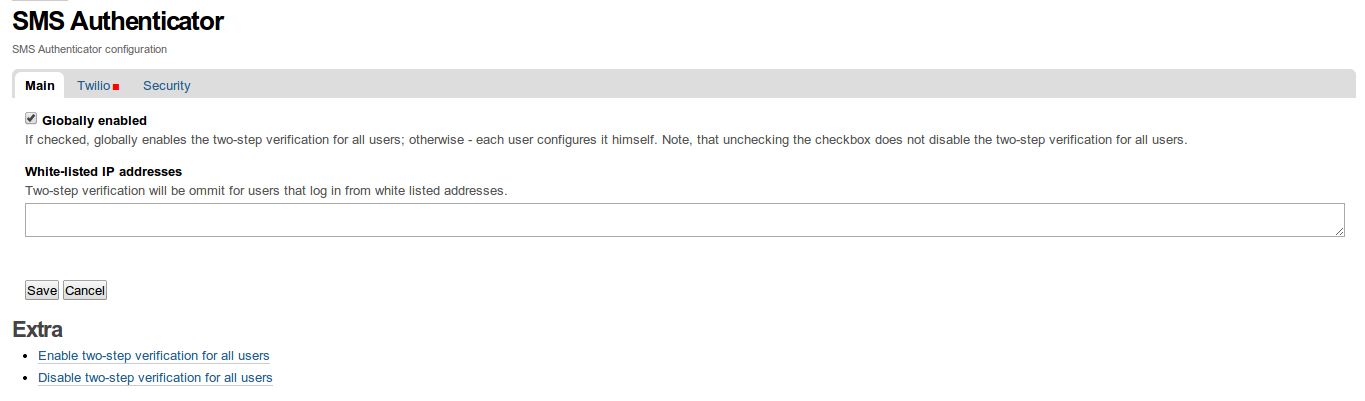
Security
Secret Key
Site secret key - can be any string. See it as some sort of a password.
Token lifetime
Lifetime of the login- and the mobile number reset- codes. Defaults to 5 minutes (300 seconds).
Notes
It’s important that SMS Authenticator comes as first in the ZMI -> acl_users -> Authentication.
Tested in combination with the following products:
The Products.LoginLockout. SMSAuthenticator comes as first, LoginLockout as second. All works fine.
Documentation
See the documentation at:
Support
For feature requests or bugs, open an issue. For questions, send us an email to info@gw20e.com.
License
GPL 2.0
TODOs and Roadmap
See TODOS.rst file for the list of TODOs.
Changelog
0.3.5 (unreleased)
0.3.4 (2018-03-16)
Added support for Messagebird SMS gateway provider. For now, quite hard-coded, could be made more pluggable. [JJM]
0.3.3 (2017-03-10)
use the correct memberdata property in the login-formcontroller-script. (this used to work on a plone 4.3.9 portal, but broke the login process on 4.3.11) [fRiSi]
0.3.2 (2016-05-25)
Set the default value of enable_two_step_verification for new users to the registry setting ISMSAuthenticatorSettings.globally_enabled (see issue #15) [pcdummy, fRiSi]
Expand the uninstall functionality with proper removal of persisent objects [puittenbroek]
Better error logging [puittenbroek]
Don’t logout user when doing a POST [puittenbroek]
Allow admin’s to change fields on the user’s profile [puittenbroek]
Add a whitelist of user’s who are excluded from two factor [puittenbroek]
Use newer version of Twilio api (=> 5.4.0) so we can see the ‘Delivered’ status [puittenbroek]
pep8 some files [puittenbroek]
Only enable two factor for all users if it was actually changed, turned on [puittenbroek]
Always sent a (new!) code upon login [puittenbroek]
0.3.1 (2015-02-12)
Clean product uninstall (also the PAS plugin). [barseghyanartur]
Soften dependencies.
0.3.0 (2014-10-06)
Make it possible to resend a token in case if the SMS message got lost on the way. [barseghyanartur]
0.2.9 (2014-10-03)
Fix: CL adduser fails due to plone.api, but adduser adds as a Zope account, which doesn’t need the twofactor properties. We shortcut the subscriber if it’s a Zope account being added. See plone.api docs for issue with ‘scripts’: http://docs.plone.org/external/plone.api/docs/api/exceptions.html#plone.api.exc.CannotGetPortalError [puittenbroek]
0.2.8 (2014-07-07)
Use source_users IAutheticationPlugin for password check to prevent recursive loop [puittenbroek]
Better return values, we always return None in our pas plugin [puittenbroek]
Add ‘enableAutoFocus’ forms to enable auto focus [puittenbroek]
0.2.7 (2014-06-20)
Direct user to a ‘reset email sent’ page instead of loginfom [puittenbroek]
Improve/change some help texts [puittenbroek]
0.2.6 (2014-06-19)
Improved help texts. [barseghyanartur]
0.2.5 (2014-06-18)
- Adding admin helper views for viewing IPs that users have been using when logging in.
[barseghyanartur]
0.2.4 (2014-05-08)
Increasing number of chars in the SMS token from 6 to 8. [barseghyanartur]
0.2.3 (2014-03-20)
Number of fixes and improvements. [barseghyanartur]
Fixes in translations. [barseghyanartur]
0.2.2 (2014-03-10)
Fixed lost Plone info status message on mobile number (re)set. [barseghyanartur]
0.2.1 (2014-03-10)
Better success message on mobile number (re)set. [barseghyanartur]
0.2 (2014-03-10)
Taking out an extra step with logging in for the first time. Instead, logging it the user after the confirmation of the mobile. [barseghyanartur]
Having the username filled in setting up the mobile number for the first time, since at that point it’s already known. [barseghyanartur]
0.1 (2014-02-28)
Initial release, with two-step verification, IP white-listing, configurable lifetime for the login codes, mobile number recover and app control panel. [barseghyanartur]
Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Hashes for collective.smsauthenticator-0.3.4.tar.gz
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 | 75dc3b8d28e1f596d16b7961150412c10c11b1adc70d7d8d1357c86801c0052b |
|
| MD5 | 5639f96e7d4bf0056757a079e670b45e |
|
| BLAKE2b-256 | 1f178ac2489881088193bbc6795abd245a9dc34f3c5b739cafd498edce78a2fe |













